Analysis of MQTT Protocol used for secure IoT device communication, need for light weight crypto, et cetera.
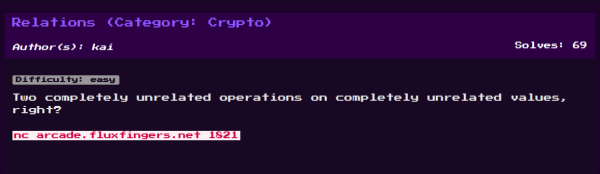
Hack.lu CTF 2018 Crypto Writeups
Hack.lu CTF is over and we (@teambi0s) finished 13th globally and since we were registered as a local team (thanks to @GeethnaTk) and stood first among the teams registered locally, hence we are eligible for prizes! Yay! This blog post covers detailed solutions to two of the crypto challenges from Hack.lu CTF 2018- Relations and... Continue Reading →
InCTF International 2018- Crypto Writeups [Part-2]
Intended solutions of two crypto challenges from InCTF International 2018: Request-Auth and EC-Auth
InCTF International 2018- Crypto Writeups [Part-1]
Write-ups of two crypto challenges from InCTF-2018: Throwback and Baby-Alice-Bob
Announcing Crypton- An educational library to learn offensive and defensive crypto(graphy)!
In this blog post, I will be talking about my new library Crypton, my journey of building this library, future plans and much more! Check out the library on GitHub: https://github.com/ashutosh1206/Crypton Introduction This library is an attempt by the author to help provide a platform to learn and practice Offensive and Defensive cryptography for people interested... Continue Reading →
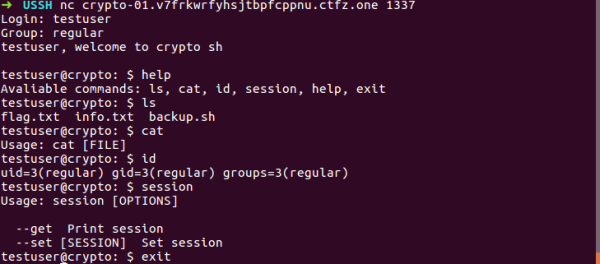
Exploiting cookie auth mechanism: CTFZone USSH-3.0 write-up
In this post, I will be discussing my solution for USSH-3.0 challenge from CTFZone which I think is the unintended way. The challenge was quite peculiar involving "blind" exploit as you will see in this write-up. Some parts of the challenge might look like guessing, but if you read this write-up start-to-end, you will see... Continue Reading →
ASIS CTF Quals 2018: Crypto Write-ups
Write-ups of 2 Crypto challenges from ASIS CTF Quals 2018- Uncle Sam(123 points) and OPEC (207 points)
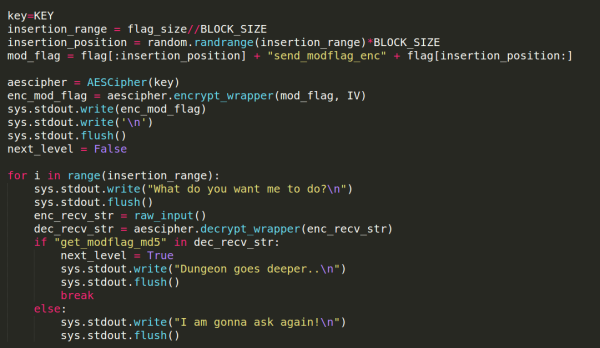
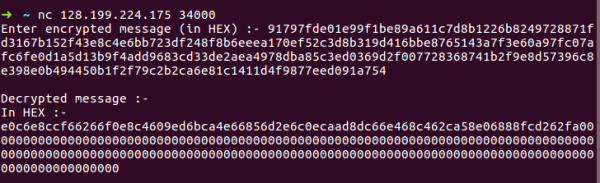
Swamp CTF 2018- Locked Dungeons-2 Write-up
CBC Bit Flipping Attack + Vulnerable unpadding function + Byte by Byte decryption
Pragyan CTF- RSA’s Quest
Points: 200 Description: Rivest comes up with an encryption, and Shamir creates a service for decrypting any cipher text encrypted using Rivests’s encryption. Adleman is asked to decrypt a specific ciphertext, but he is not able to do so directly through Shamir’s service. Help him out. This CTF had some okay-ish crypto challenges(didn't like the first... Continue Reading →
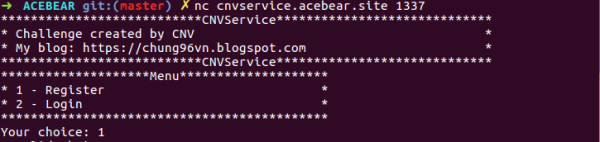
CNVService- AceBear CTF 2018 Writeup
This challenge was by far the most interesting and tricky Bit Flipping Attack I had come across, and I couldn't resist but share the write-up of this challenge. The challenge is one of the best illustrations of Bit Flipping Attack on Chained Block Cipher modes so, it is highly recommended for people who want to get... Continue Reading →